Introduction – What Is Zero Trust Security?
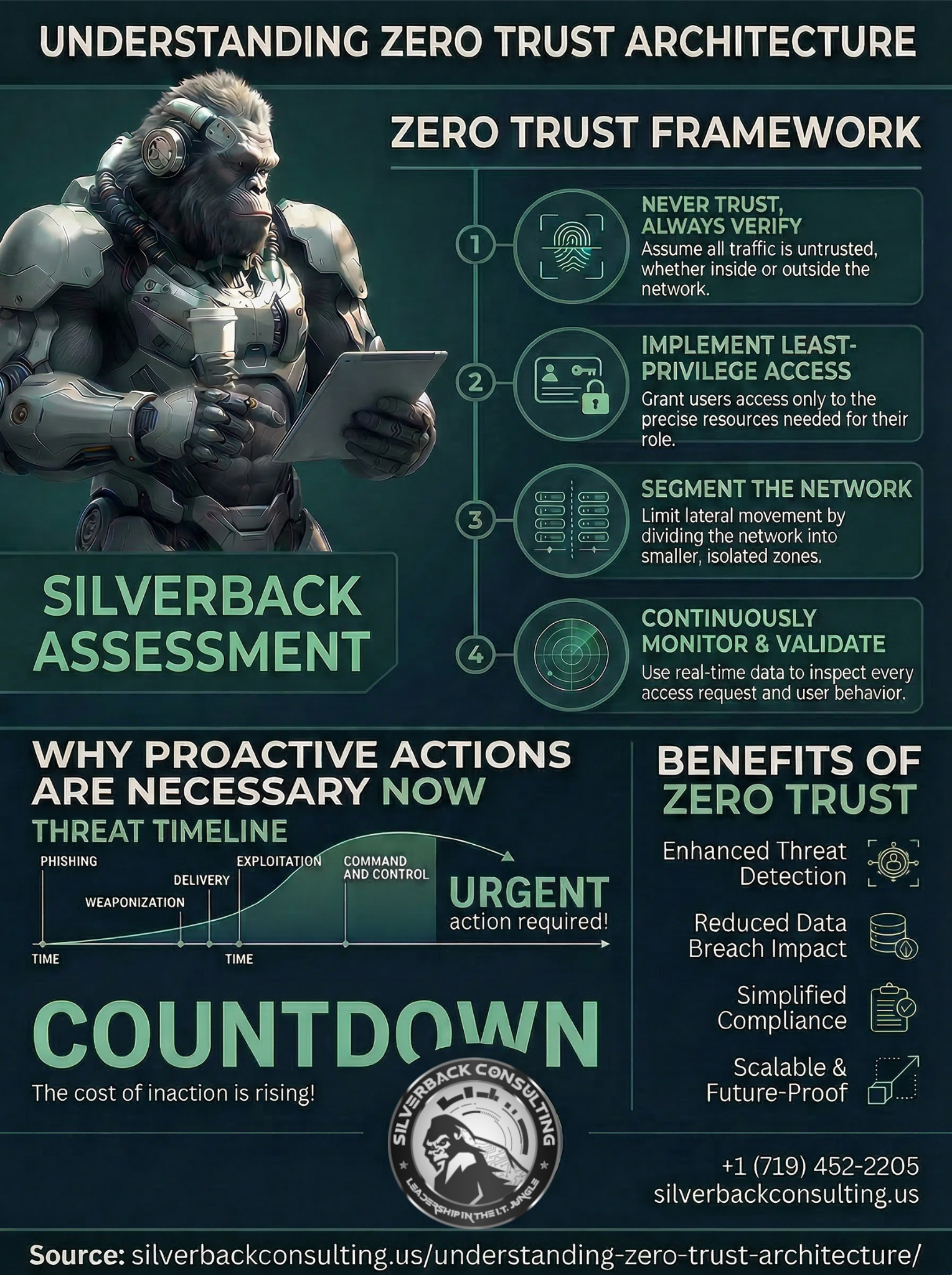
Zero trust is a cybersecurity model based on one simple principle:
Never trust. Always verify.
Traditional security models assumed that once a user entered the network, they could be trusted. This model worked decades ago when networks were centralized and employees worked primarily inside offices.
Today, environments are completely different:
- Employees work remotely
- Cloud applications host sensitive data
- Third-party vendors connect to internal systems
- Attackers steal credentials through phishing
- Malware spreads laterally across networks
Because of these realities, trusting anything automatically creates risk.
A zero trust architecture removes implicit trust entirely. Every request to access a system, application, or piece of data must be verified continuously.
Verification typically includes:
- Identity authentication
- Device health validation
- Location analysis
- Behavioral monitoring
- Access policy enforcement
Only after these checks pass is access granted, and even then, access is limited.
How Zero Trust Protects Your Business ▼
Why Is Zero Trust Critical in Modern Cybersecurity?

Cyberattacks are becoming more sophisticated and damaging every year.
Many major breaches occur because attackers gain a single foothold and then move freely inside the network.
Zero trust stops this lateral movement.
Instead of broad access privileges, zero trust architecture restricts users and systems to the minimum access required.
This approach protects organizations from several major threats:
Credential Theft
Stolen passwords alone cannot grant access if multi-factor authentication and contextual verification are required.
Ransomware
Ransomware spreads rapidly across flat networks. Zero trust segmentation prevents this movement.
Insider Threats
Employees or compromised accounts cannot access sensitive systems without proper authorization.
Third-Party Risks
Vendors and contractors receive restricted, monitored access only to necessary systems.
By enforcing strict verification at every step, zero trust significantly reduces the attack surface.
What Are the Core Principles of Zero Trust Architecture?
A strong zero trust architecture follows several foundational principles that guide security policies and technology deployment.
1. Verify Every Identity
Users must prove their identity before accessing any system. This usually includes:
- Multi-factor authentication (MFA)
- Identity provider verification
- Risk-based authentication
Verification does not occur only once. Zero trust continuously validates identity during the entire session.
2. Enforce Least Privilege Access
One of the most powerful elements of zero trust is limiting access rights.
Users receive only the permissions necessary to perform their job functions.
For example:
- Finance staff access accounting systems
- Healthcare providers access patient records
- IT staff manage infrastructure
But no one receives unrestricted access.
This dramatically reduces the impact of compromised accounts.
3. Assume Breach
Zero trust assumes attackers may already be inside the environment.
Therefore organizations must:
- Monitor all activity
- Analyze behavioral patterns
- Detect anomalies quickly
Continuous monitoring allows security teams to detect suspicious behavior before damage spreads.
4. Micro-Segmentation
Networks are divided into smaller protected zones.
This technique prevents attackers from moving freely between systems.
For example:
- Finance systems separated from HR systems
- Clinical data isolated from general business networks
- Administrative access restricted to specific environments
Micro-segmentation is a cornerstone of effective zero trust architecture.
5. Continuous Monitoring and Analytics
Security tools constantly analyze activity across the environment.
This includes monitoring:
- User behavior
- Network traffic
- Application access
- Endpoint activity
Advanced security analytics and threat detection systems identify anomalies quickly and trigger automated responses.
What Technologies Enable Zero Trust Architecture?
Implementing zero trust requires a combination of security technologies working together.
Key components typically include:
Identity and Access Management (IAM)
Centralized identity systems verify users and manage permissions.
Multi-Factor Authentication (MFA)
Users must confirm their identity through multiple verification methods.
Endpoint Detection and Response (EDR)
Endpoints such as laptops and servers are monitored for suspicious behavior.
Secure Access Service Edge (SASE)
Cloud-delivered security platforms enforce policies regardless of user location.
Network Micro-Segmentation
Internal network controls limit system-to-system communication.
Security Information and Event Management (SIEM)
Centralized logging and analytics detect threats across the environment.
Together, these technologies create the foundation of a comprehensive zero trust architecture.
How Does Zero Trust Prevent Cyberattacks?

Organizations often ask whether zero trust actually stops attacks.
The answer lies in how it disrupts the attack lifecycle.
Step 1: Prevent Unauthorized Access
Attackers cannot access systems without authentication and verification.
Step 2: Limit Access Privileges
Even if an attacker compromises credentials, least-privilege policies limit damage.
Step 3: Detect Suspicious Activity
Monitoring tools detect abnormal behavior immediately.
Step 4: Contain the Threat
Micro-segmentation prevents attackers from spreading across the network.
By breaking multiple stages of the attack chain, zero trust dramatically reduces breach impact.
How Can Small and Mid-Sized Businesses Implement Zero Trust?
Many organizations assume zero trust architecture is only for large enterprises. In reality, small and mid-sized businesses benefit just as much, if not more.
A practical implementation typically begins with several foundational steps.
Step 1: Strengthen Identity Security
Deploy multi-factor authentication across all accounts.
Step 2: Audit Access Permissions
Remove excessive privileges and enforce least-privilege policies.
Step 3: Secure Endpoints
Ensure devices are monitored and protected with endpoint detection tools.
Step 4: Protect Email Systems
Email remains the most common entry point for cyberattacks.
Step 5: Monitor Network Activity
Visibility is essential for detecting threats early.
At Silverback Consulting, we help organizations implement zero trust architecture strategies that are practical, scalable, and cost-effective.
How Does Zero Trust Support Compliance Requirements?
Many regulatory frameworks emphasize principles aligned with zero trust security.
Examples include:
- HIPAA
- NIST Cybersecurity Framework
- CMMC
- SOC 2
These frameworks require organizations to implement controls such as:
- Strong identity verification
- Access restrictions
- Continuous monitoring
- Audit logging
- risk management
A properly implemented zero trust architecture helps organizations meet these requirements while strengthening overall cyber security posture
Why Zero Trust Is the Future of Cybersecurity
Cybersecurity threats will continue evolving. Attackers will keep exploiting weak credentials, unpatched systems, and overly permissive access policies.
The organizations that remain resilient will be those that eliminate implicit trust from their environments.
Zero trust security transforms how organizations protect data, systems, and users by enforcing verification at every layer.
Key advantages include:
- Reduced attack surface
- Stronger identity protection
- Improved threat detection
- Limited breach impact
- Enhanced compliance readiness
For modern businesses operating in cloud environments with remote workforces, zero trust architecture is no longer optional—it is essential.
Conclusion: Strengthening Your Security with Zero Trust
Every organization faces cyber risk. The question is not whether attackers will attempt to gain access, but how prepared your security model is to stop them.
Implementing zero trust dramatically improves your ability to protect critical systems and sensitive data.
At Silverback Consulting, we specialize in helping organizations assess their cybersecurity posture and implement zero trust architecture strategies that strengthen security without disrupting operations.
The result is a more resilient, more secure business environment prepared to defend against modern cyber threats.
What are zero trust principles?
Zero trust principles are based on verifying every user and device before granting access, enforcing least-privilege access, continuously monitoring activity, and assuming that threats may already exist inside the network.
What is zero trust network access?
Zero Trust Network Access (ZTNA) is a security approach that grants users access only to specific applications or systems after verifying identity, device health, and context, rather than giving broad network access.
How to implement zero trust?
Implementing zero trust typically begins with strong identity management, multi-factor authentication, least-privilege access controls, device security monitoring, network segmentation, and continuous threat detection.
What is zero trust in cyber security?
Zero trust in cybersecurity is a security model that eliminates implicit trust by requiring continuous verification of users, devices, and applications before allowing access to data or systems.
How does zero trust work?
Zero trust works by authenticating identities, validating device security, enforcing strict access policies, monitoring activity in real time, and restricting users to only the resources they need.
What are the benefits of zero trust?
Benefits of zero trust include reduced attack surfaces, improved protection against ransomware and credential theft, stronger visibility into user activity, and better compliance with security regulations.
Disadvantages of zero trust?
Potential disadvantages of zero trust include implementation complexity, the need for careful access policy planning, and possible initial costs for upgrading identity and monitoring systems.
What are the best zero trust security solutions for small businesses?
Some of the best zero trust security solutions for small businesses include managed security providers such as Silverback Consulting, which help organizations implement zero trust architecture, identity protection, monitoring, and network segmentation.
Which companies offer zero trust network access products?
Companies offering zero trust network access solutions include security vendors and managed providers like Silverback Consulting, along with major cybersecurity platforms that provide identity verification and secure access technologies.
How do zero trust platforms integrate with cloud services?
Zero trust platforms integrate with cloud services by verifying user identities, enforcing access policies, and monitoring activity across SaaS applications, cloud infrastructure, and remote devices.
Can zero trust models improve remote workforce security?
Yes, zero trust models significantly improve remote workforce security by requiring continuous authentication, validating device health, and limiting access to only approved applications regardless of user location.
Best practices for a zero trust security model?
Best practices for a zero trust security model include enforcing multi-factor authentication, implementing least-privilege access, segmenting networks, monitoring user behavior continuously, and regularly reviewing access policies.
Ready to Strengthen Your Security with Zero Trust?
Cyber threats are evolving, and traditional security models are no longer enough. Our experts at Silverback Consulting can help you implement a practical Zero Trust architecture that protects your users, devices, and critical data while reducing your risk of breaches. Whether you’re just starting your cybersecurity journey or looking to strengthen your existing defenses, we’re here to help. Call us today at (719) 452-2205.
Silverback Consulting
303 South Santa Fe Ave
Pueblo, CO 81003
support@silverbackconsulting.us
“Leadership in the I.T. Jungle”